Building outbound links? You may have a link phishing security issue

What is an outbound link?
An outbound link in a webpage is a hyperlink that directs users to another website or web page external to the current website.
Also known as an external link, outbound links play a crucial role in connecting content across the internet and providing users with additional resources, references, or related information.
The target="_blank" security vulnerability: Still relevant in 2026
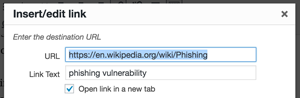
If you're building outbound links and using target="_blank" to open clicks in a new browser tab, you need to understand a security vulnerability known as "reverse tabnabbing" that can expose your visitors to phishing attacks.
Modern browsers (Chrome ≥88, Edge ≥88, Firefox ≥79, Safari ≥12.2) now automatically apply rel="noopener" to target="_blank" links. However, for maximum compatibility and security, explicitly adding rel="noopener noreferrer" is still recommended.
At DailyStory, we help businesses build trust through secure marketing campaigns. Whether you're using our URL shortener for SMS campaigns or linking to external resources in your content, understanding link security protects both your brand and your customers.
Like many websites, for outbound links we use target="_blank" in our link anchors. This opens the link in a new tab, keeping visitors on our website while they explore external content. It's a common practice in email marketing, social media, and content marketing.
However, this technique can create a security vulnerability that's particularly dangerous for businesses using SMS marketing and URL shorteners in their campaigns.
This security issue becomes more critical when combined with URL shorteners. In 2026, threat actors increasingly weaponize shortened links in phishing campaigns, making link security practices essential for any business sending marketing messages.
How to fix this vulnerability
The solution is simple but crucial. For any link using target="_blank", add the security attribute:
rel="noopener noreferrer"
Here's what a secure external link should look like in 2026:
The rel="noopener" attribute prevents the new tab from accessing the window.opener property, while rel="noreferrer" prevents the destination from seeing the referrer header and provides additional compatibility for older browsers.
This is especially important for businesses using email marketing and SMS campaigns where customer trust is paramount.
Modern CMS and platform support
Most modern content management systems now handle this automatically. WordPress has added rel="noopener" by default since 2019, and most email marketing platforms include these security attributes in their link generators.
DailyStory's URL shortener automatically implements security best practices, ensuring that shortened links in your SMS and email campaigns don't expose customers to these vulnerabilities. Our custom domain shorteners also help build trust by using your own branded domain instead of generic short links that customers might view as suspicious.
How the vulnerability works
When you use target="_blank" without proper security attributes, the newly opened tab gains access to the window.opener property, allowing it to manipulate the original tab's location through JavaScript.
This vulnerability, known as "reverse tabnabbing," has been used in attacks against major platforms, though most have now implemented protections.
Modern attack scenarios
Here's how a modern attack might work: You receive an SMS or email with a shortened link to an article about "Revolutionary Marketing Strategies." The link opens in a new tab, and while you read the article, malicious JavaScript redirects the original tab to a fake login page.
When you finish reading and return to the original tab, you see what appears to be your email provider asking you to log in again. Trusting the familiar URL bar (which may be disguised), you enter your credentials directly into a phishing site.
Why URL shorteners amplify the risk
URL shorteners make this vulnerability particularly dangerous because they hide the destination URL. Users can't verify where they're going before clicking, making them more susceptible to malicious redirects.
According to cybersecurity research, phishing attacks using shortened URLs increased significantly through 2025-2026, with attackers specifically targeting SMS campaigns and email marketing links.
This is why DailyStory recommends branded domain shorteners for high-volume SMS campaigns. When customers see links from your familiar domain rather than generic shorteners like bit.ly, they're more likely to trust and click your links while being naturally suspicious of unfamiliar domains.
Best practices for marketing campaigns
- Always use
rel="noopener noreferrer"on external links withtarget="_blank" - Use branded domain shorteners rather than public services like bit.ly
- Implement security scanning for links in your marketing campaigns
- Monitor for suspicious click patterns that might indicate compromised links
- Educate your audience about recognizing legitimate links from your brand
Whether you're running SMS campaigns, email marketing, or content marketing, protecting your links protects your customers and preserves the trust you've built with your audience.
Frequently Asked Questions
What is reverse tabnabbing?
Reverse tabnabbing is a phishing technique where a page opened via target="_blank" uses the window.opener JavaScript property to redirect the original tab to a malicious page — typically a fake login screen. The user returns to the original tab, sees a familiar-looking site asking them to sign in again, and enters credentials directly to the attacker.
Is target="_blank" still dangerous in 2026?
The risk is significantly reduced because modern browsers (Chrome 88+, Edge 88+, Firefox 79+, Safari 12.2+) now apply rel="noopener" implicitly to any link that opens in a new tab. However, explicitly adding rel="noopener noreferrer" is still recommended for older browsers, email client renderers, embedded webviews, and defense-in-depth.
What is the difference between rel="noopener" and rel="noreferrer"?
rel="noopener" prevents the new tab from accessing window.opener, which blocks reverse tabnabbing. rel="noreferrer" does the same and strips the Referer header so the destination site cannot see which page sent the visitor. Using both (rel="noopener noreferrer") is the safest default for external links.
Do I still need rel="noopener" if modern browsers add it automatically?
Yes, for three reasons: older browsers and webviews do not apply it, some email clients render HTML outside a modern browser engine, and explicit attributes make your security posture auditable. Adding it costs nothing and guarantees the protection regardless of where the link is rendered.
How do URL shorteners amplify phishing risk?
Shorteners hide the destination URL, so recipients cannot visually verify where a link leads before clicking. Attackers exploit this in SMS and email campaigns using generic shorteners like bit.ly. Using a branded domain shortener signals authenticity and makes malicious look-alike links easier for recipients to spot.
Will adding rel="noopener noreferrer" hurt my SEO?
No. Google has confirmed that noopener has no impact on how link equity is passed. noreferrer does suppress the referrer header, which can affect third-party analytics on the destination site, but it does not affect search rankings or crawling.
Does WordPress add rel="noopener" automatically?
Yes — WordPress has automatically added rel="noopener" to any link inserted through the block editor with "Open in new tab" enabled since version 5.1 (2019). Most modern CMS platforms and email marketing tools now do the same. Legacy content and custom-coded templates are where the vulnerability typically still hides.
Want to ensure your marketing campaigns use secure, trustworthy links? DailyStory's URL shortener includes built-in security features and branded domain options to keep your campaigns both effective and secure.